The previous article (API Security, Part 1) discussed some of the challenges in protecting APIs from hostile traffic, and gave an overview of Curiefense’s approach. Now in this article, we’ll discuss these security mechanisms:
(This feature is pending in the next release of Curiefense.)
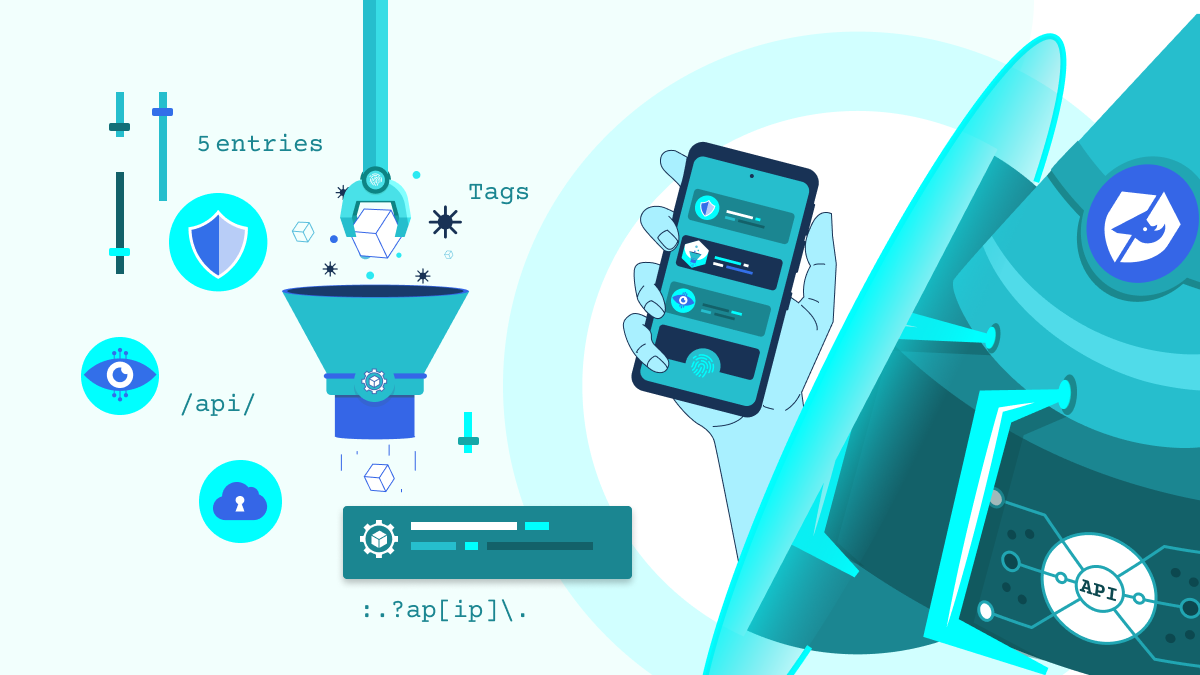
The Profiling mechanism (discussed here) includes a default ruleset to identify API usage. If you customize it to match your APIs, as shown in the UI screenshot above, it creates an easy way to identify incoming calls.
This has several uses, including:
Curiefense can block API calls based on the identity of the caller. Examples:
Curiefense can also exempt API calls from filtering based on defined characteristics. Example: calls coming from internal IPs.
Mobile/native apps present an interesting situation. On the one hand, they are API clients, and so they will be secured by the usual filtering of API traffic. However, we realized that these apps present an opportunity for additional protection.
As a result, Curiefense offers an optional SDK for iOS and Android apps, which are rebuilt and published with the SDK embedded. In use, the SDK signs the application, authenticates the device, hardens all communication, and verifies user identity.
This provides a reliable, secure mechanism to verify that the packets are originating from a legitimate user, and not from an emulator or other bot.
This category includes several different mechanisms, including rate limiting, API session flow control, and behavioral profiling / API abuse prevention.
You can configure Curiefense to block all API calls that exceed a specific limit within a certain period of time.
(“Limit” usually refers to the number of calls made by a traffic source, but it can also be defined as the number of calls made with a specific header, cookie, argument, attribute, etc.)
This mechanism protects APIs against a wide variety of attacks, including:
In the final article in this series, we’ll discuss API session flow control, behavioral profiling, content filtering, hostile bot detection, and deep packet inspection.